When I first started looking at VPNs, I noticed a feature on some of them called a Kill Switch. I decided to find out more about this kill switch feature and see whether it was essential to protecting my privacy.
What is the kill switch on a VPN? A kill switch is a VPN feature designed to stop all internet connectivity if the VPN connection fails. The kill switch automatically resumes internet connectivity when the VPN connection is back up. The kill switch protects against identifying information being exposed to the internet if the VPN connection fails.
When connected to the internet using a VPN, the IP address the internet sees, will be the one assigned by the VPN service provider. This will also mean whatever sites are visited across the internet, these will only be known to the VPN provider, and as long as they don’t keep any logs. There will not be any history of what sites have been visited, including the date of the visits and the exact time the sites were visited.
With the VPN running, your Internet Service Provider (ISP) has no idea of your activity as they will only see a connection to your VPN provider in their own logs. So, while the VPN is running, the chances of remaining anonymous on the internet are greatly increased.
More so if a good VPN is used which has leak protection against DNS and WebRTC leaks, you could end up being totally invisible on the internet.
VPN connection failure
Where a VPNs protection of keeping their customers anonymous falls apart, is when there is a VPN connection failure, and believe me, this is not a rare occurrence. Most of the VPNs I have used have at some time failed and required restating the VPN connection to work again.
Many times, I have not even realised the VPN connection has failed and only realised when I have noticed the VPN icon in the system tray is not green anymore. So, during this time I have run the risk of exposing my identity to the internet including to my ISP.
All the websites I have visited during the VPN connection failure will in all likelihood been left as part of logs my ISP undoubtedly keeps logging all my activity.
Torrenting at night
Leaving a VPN running all night, downloading away from a torrenting website, could lull most people into thinking no one will ever know what they are downloading, other than themselves. However, if the VPN connection fails even for a few seconds, others will start to know what they are downloading.
Starting with the ISP, as instead of the VPN DNS servers being used for name resolution, the internet connection will default automatically to use the ISPs DNS servers.
These DNS servers will log all the sites visited, as they are used to translate the name of the site the connection is being made to, into a unique number (octet format) which allows the connections to be made to the correct location on the internet.
So when I connect to the website http://www.google.com, the DNS servers have a list of the IP address matching the name www.google.com. In the screenshot below you can see how I was able to find out one of the IP addresses for www.google.com to be 172.217.169.36. By typing this address into my web browser, I still get the www.google.com home page.
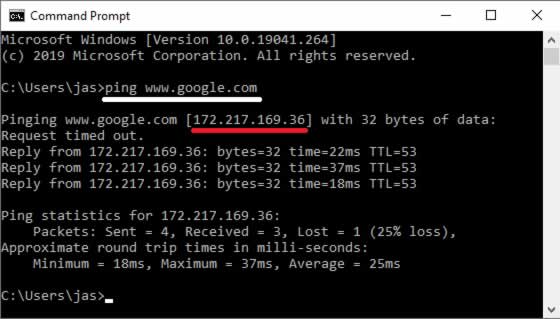
It’s the IP address the copyright holders’ legal teams use as a starting point to find out who was illegally downloading their copyrighted works from a torrent website.
If the only IP address they have is the one from a VPN, the chances of a VPN giving up the customer details associated with the IP address could be remote (some VPNs do still give up their customers to legal authorities, so it’s best to choose one with a robust privacy policy and track record).
However, the IP address owned by the ISP, if that’s found out to be associated with the illegal downloading from a torrent site, the copyright holders may find it much easier to get a court order, forcing the ISP to tell them which one of their customers was using their IP address at the time of the alleged offence.
Use a VPN kill switch
Enter the kill switch feature which will automatically cut all internet connectivity, should the VPN connection fail (check out my latest list of VPNs with kill switches). Stopping all connections being made to the internet when there’s no VPN protection.
When the VPN connectivity resumes, the kill switch will automatically allow the internet connectivity to resume, thereby making sure no communication has been made to the internet without first going across the VPN connection.
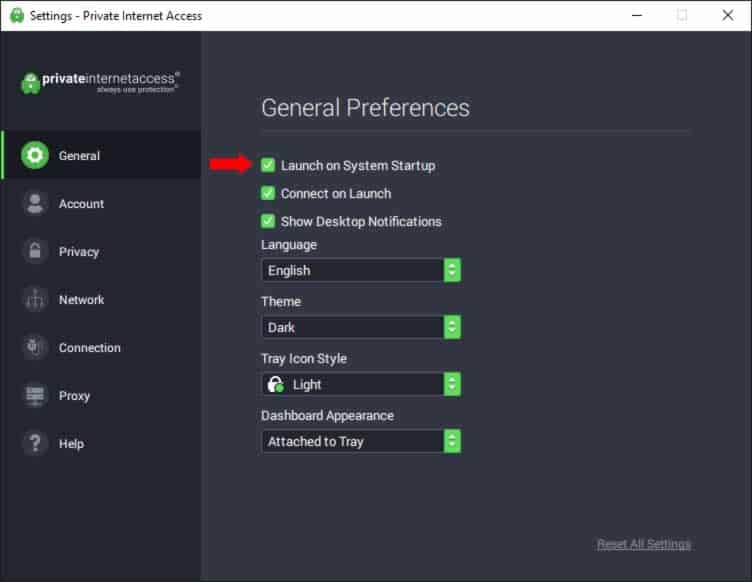
For better protection, it is best to set the VPN to start up automatically as soon as the device has finished booting up and at the same time, make the kill switch feature come on automatically too. So, a computer running Microsoft Windows will start the VPN software as soon as the login has been completed, and then the kill switch will automatically start as the VPN starts.
With automatic starting of the VPN and kill switch, when any connection is made to the internet, the kill switch will automatically check to see if the VPN is connected to a VPN server before allowing any of the internet bound traffic to pass across the VPN.
If the VPN and the kill switch feature are enabled after the internet connection is made, any internet bound traffic initiated before hand will be identifiable as the IP address assigned by ISP will be used in communications to internet sites and not the IP address assigned by the VPN service.
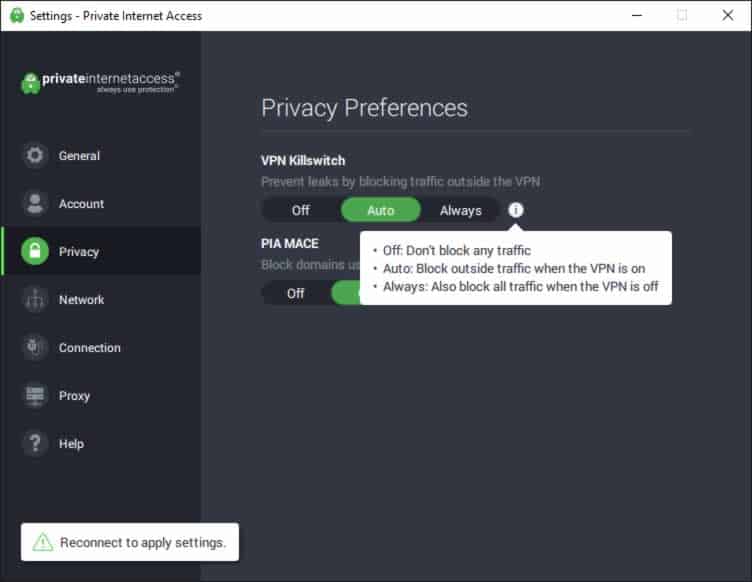
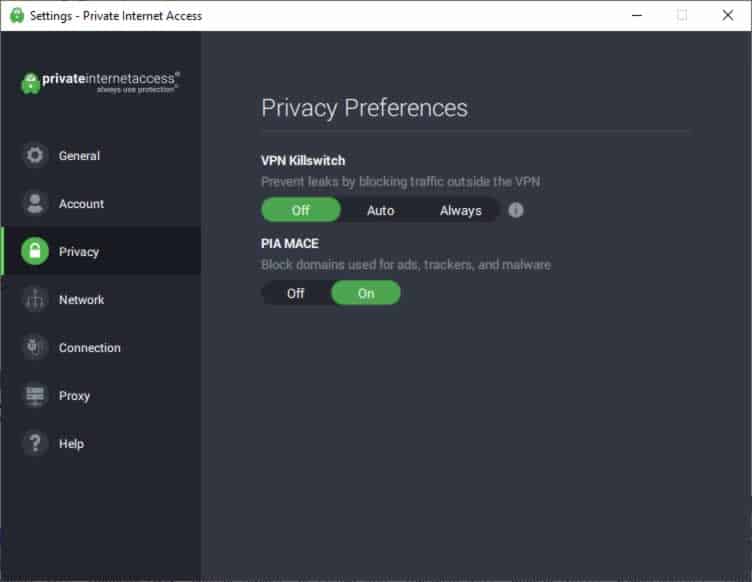
My VPN has three options for the kill switch, with ‘Auto’ for starting the kill switch automatically when I start the connection to the VPN server. ‘Always’, so the VPN is always switched on, when the VPN software is running and the ‘Off’ setting, which as the name implies, means the kill switch is not running.
I have also made sure the VPN starts up automatically when my computer’s operating system, Microsoft Windows in this case, has allowed me to login.
VPN connection failed?
VPN connections do fail from time to time and I have stated earlier this can be quite common. There are a number of potential reasons why the VPN connection can fail including:
- Conflicts with other software
- VPN protocol reliability
- VPN server overloading
- VPN sever failure
Conflicts with other software
VPN connection failure can result from conflicts on devices with other software like Anti-Virus software. This type of software regularly scans devices and it is during this scan, it could cause the VPN to fail.
Adding an exception to the Anti-Virus software not to scan the VPN software could help in protecting against VPN failures but this could become cumbersome, if other software products like firewalls, spyware and general malware programs also require exceptions. The kill switch is just a more elegant way of dealing with VPN connection failures.
VPN protocol reliability
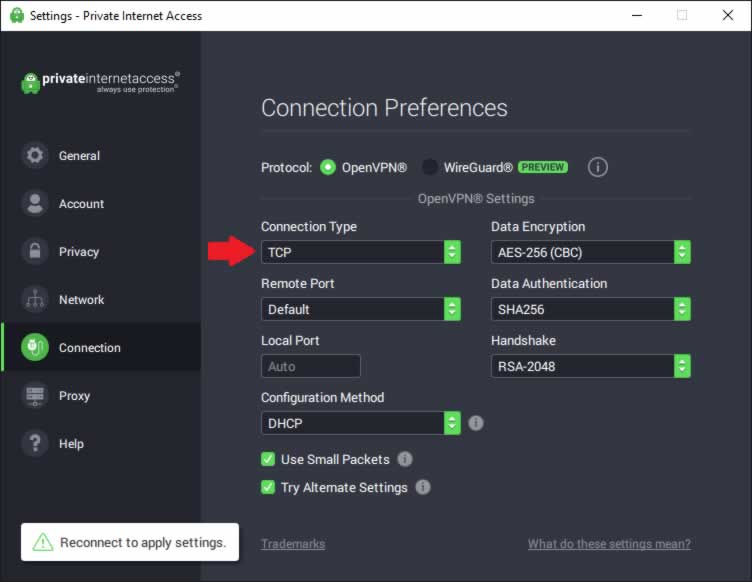
The VPN connection protocols can also make a difference in the reliability of connections with connection made using the UDP protocol being less reliable than using the TCP protocol. Mainly due to more error checking being done with the TCP protocol compared to the simpler UDP protocol. I tend to set my VPN connections to always use the TCP protocol.
VPN server overloading
The VPN server you have connected to could also become overloaded, especially if the region you are connecting to, only has a limited number of VPN servers available. This may hold true for smaller jurisdictions so it maybe more prudent to select VPN servers in the larger regions.
Typically, the VPN servers are hosted in third party data centers, so having to use an expensive data center may mean having to compromise on the total number of VPN servers made available to VPN customers.
VPN Server failure
The current VPN server you are connected to could easily fail, as there maybe a power outage or a component on the VPN server could fail. Actually, the VPN server is most likely to be a virtual server running on a physical server, so a network card failing or a hard disk failing, could cause an interruption in the VPN connection being made.
If the VPN connection is set to auto connect during any failure, the time taken to re-establish the VPN connection, could be enough time for identifying information like the IP address, as this could easily leak out for just enough time, to give the identity away.
I have worked for many large companies and regularly visited their data centers, where system components failing is more common than most people think.
I used to use a VPN service which was terrible at maintaining connectivity, with my VPN connections frequently dropping out and the whole experience being incredibly slow, as the VPN servers were overloaded.
I even set up my own VPN server once and because the Virtual Private Server (VPS) I rented was so cheap, the customer service itself was quite poor. I remember one day, the hosting company decided to move my VPS server from one of their physical hosts to another, without warning me and I lost my VPN connectivity for a couple of hours.
If I’d been using the VPN in anger, my connection would have stopped and my browsing activity would have been visible to my ISP.
How to test a VPN kill switch?
The easiest way to test a VPN kill switch is to:
- connect to any website
- Switch on the kill switch on the VPN
- Disconnect the VPN connection
- Refresh the website connected to in step 1.
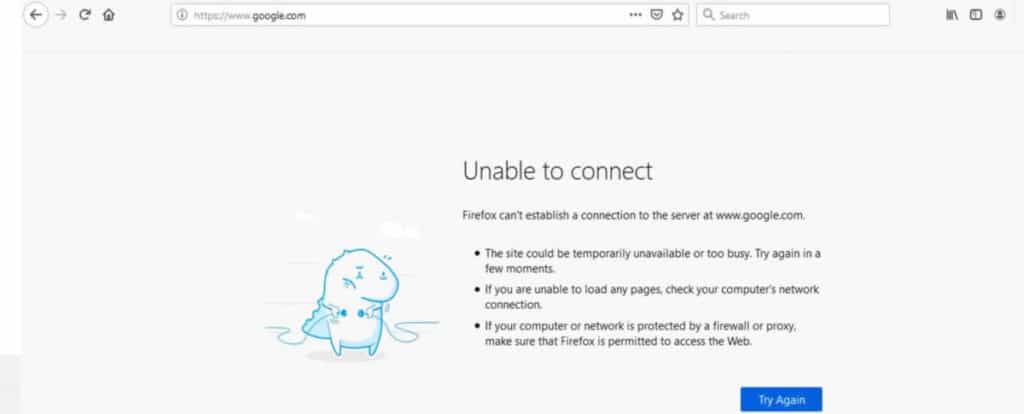
If everything has worked as expected, the website you have connected to will not be visible anymore instead you will have an error being displayed in your web browser, similar to the picture below.
How do I disable VPN kill switch?
Disabling the kill switch is as easy as setting it up, with most VPN software having the switch to switch off. With the VPN I use, there’s an option to switch off the kill switch and at the same time, the VPN software remembers this for the next time the VPN is used, so it does not need to switched off everytime the VPN is used.
Does OpenVPN have a kill switch?
OpenVPN does not have a kill switch feature akin to those provided by the popular VPN vendors like NordVPN, ExpressVPN to Private Internet Access. However, depending on the operating system being used, firewall rules can be set up accordingly to only allow connections made through OpenVPN based on a predetermined port.
As I am not firewalling expert, this would require some technical knowledge in firewall configuration to be able to work effectively.
Conclusion
To provide stronger protection for keeping your identity anonymous during internet communications, a kill switch is an excellent even vital feature. Having the kill switch enabled automatically will ensure anytime the VPN connection to the VPN server is interrupted, no communication across the internet will be possible until the VPN connection resumes.

