
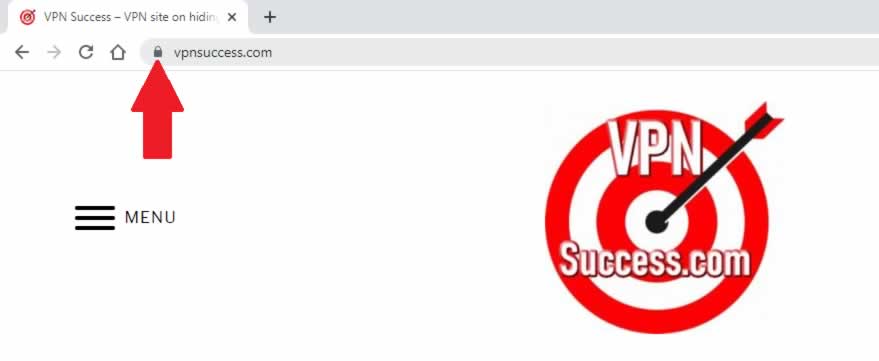
It is common practice for me to check I only connect to websites using HTTPS in the website name. I also look out for the padlock icon in the web browser address bar to give me reassurance my connection is secure even when I’m using my VPN.
Can a VPN really see HTTPS traffic? A VPN cannot see HTTPS traffic between a web browser and a website, as this is end-to-end encryption. Without knowing the cryptography key used for the encryption, the VPN will not be able to decrypt the HTTPS traffic so won’t be able to see any information passing through it.
Web traffic passing through the VPN that is not encrypted using HTTPS, such as standard web traffic using HTTP, will be clearly visible to the VPN. To protect your privacy, it’s essential to only connect to websites which support HTTPS and avoid websites which only support HTTP.
This is especially true if you are entering sensitive information using the websites forms. For example, connecting to a visa website which doesn’t use HTTPS, will mean it is quite possible for the VPN to see your passport details as well as your personal details including your date of birth, your parents details, work details and so on.
VPN can still steal your information
Even if you are using HTTPS to make connections to a website, it’s still possible for some VPNs to steal your information. This is especially true of bad VPNs designed to steal information by installing spyware on your computer or other device like a smartphone.
This spyware actively probes your web browser, looking at information you are entering on the forms on the websites you are connecting to. So, if you are logging on to your bank website, the connection will most definitely be using HTTPS (if it’s not, you need to change your bank).
So, all information sent from your web browser to the bank website will be securely sent and protected from your VPN. However, the information being typed into the web browser, may be captured by the bad VPNs spyware and send back to the VPN without you ever realizing.
This is why it is vitally important to make sure the VPN you use if trusted and reputable, check out my list of trusted VPNs here.
VPN Extensions and plugins
I’m not a fan of VPN extensions or plugins that can be easily added to popular web browsers as these VPNs can get access to the web pages being browsed and therefore potentially the information being entered.
There is many unscrupulous and malicious VPN extensions and plugins available, leading to a higher risk of personal information being stolen. Some can actually misdirect and send you to websites that look like the website you are connecting to, but instead it’s actually a fake website designed to capture your personal information.
I would always use a VPN client from a trustworthy VPN provider as it will not only provide me reassurance my information is not being spied on but also my privacy is totally protected, as all my internet traffic from my computer is passing over the VPN and not just my web browser traffic.
Weak encryption
It is quite easy to break weak encryption using specialist techniques and hacking tools, but this isn’t a problem today as it was in the past. With web browsers carefully checking websites to see if the encryption standards they use are strong and robust enough to ensure the users connecting to the website remains secure.
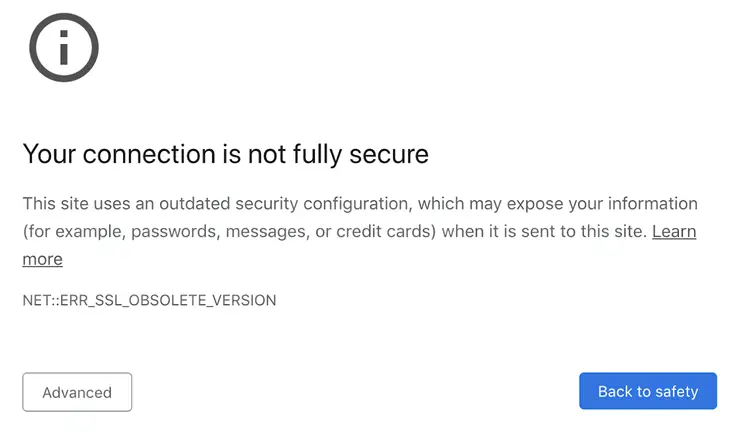
Older HTTPS encryption standards using Secure Sockets Layer (SSL) have been deemed to be insecure and new standards using Transport Layer Security (TLS), are only secure if versions 1.2 or later are used (correct at the time of writing).
Don’t worry too much about SSL and TLS, as web browsers like Mozilla Firefox, Google Chrome, Apple Safari to Edge Browser all have some level of detection of weak encryption being used.
These popular web browsers will warn you not to proceed as there is a potential security risk in using the website especially if sensitive information is going to be used.
What is HTTPS and how does it work?
When you make a connection to a website by prefixing https to the website, like connecting to https://vpnsuccess.com instead of http://vpnsuccess.com. The web server where the vpnsuccess.com website is located (hosted), sends back a certificate.
The web browser now does two checks to ensure the website can be trusted.
1. Check certificate is valid
Your web browser will check to see if the certificate is valid by looking to see if the owner of the certificate matches the website address you entered.
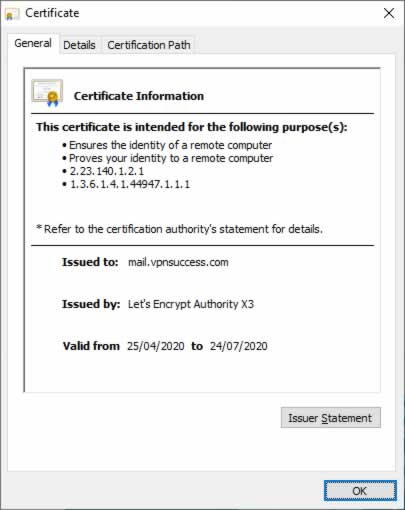
As you can see from the picture above, the owner of the certificate is mail.vpnsuccess.com, so if the website address has mail.vpnsuccess.com in it, then the certificate is valid. Also, alternative names such as just vpnsuccess.com and www.vpnsuccess.com are also valid, as they are also included in the certificate, as shown in the picture below.
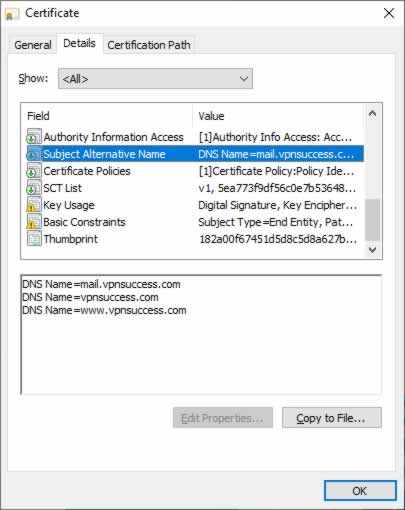
These alternative certificate names ensure slightly different variations of the website name can be used, so mail.vpnsuccess.com could be used for email security, www.vpnsuccess.com could be used for a website (it’s not used by me though, I could do at a later stage if I wanted to).
2. Check certificate is trusted
Any certificate used for encryption needs to be trusted, to make sure it follows a set of criteria. Some certificates like those classed as Organization Validation and Extended Validation offer higher standards to ensure the untrustworthy or malicious people just can’t get hold of these types of certificates to defraud people.
The certificate used on the vpnsuccess.com website is a domain validated certificate, designed to ensure you are connecting to vpnsuccess.com and not some other website when you type in vpnsuccess.com into your web browser.
This is important as sometimes people pay little regard to the website name in their web browser address bar and malicious attackers could use this to make people think they are connecting to trusted websites, when in fact they are not.
Handshake
As part of the initial HTTPS connection, there is a handshake, almost like an introduction between the web browser and the website. This handshake process known as the Hello phase, allows the web server to send information like the certificate for the website being connected to and what ciphers it can use for encryption.
Key Exchange
The communication between the web browser and the website will be encrypted but the cryptography key used for encryption needs to be securely exchanged between the website and the web browser. If a malicious VPN got hold of this encryption key, the VPN would quite easily be able to decrypt the encrypted traffic and see all the information being sent from the web browser to the website.
To ensure the encryption is strong and secure, the web browser generates a random key to be used for the encryption of traffic between the web browser and the website. It encrypts the random key using an algorithm also prescribed during the initial handshake (hello phase), and the websites public key (found on the certificate associated with the website). This encryption is known as Public Key Infrastructure (PKI) encryption.
The web browser sends this encrypted key to the website, where it’s decrypted using the websites private key allowing the key exchange to be done securely. Both the web browser and the website are now not only agreed they trust each other but have also agreed securely on a cryptographic key to encrypt the information they will be sending to one another.
Secure data exchange
Now armed with the encrypted key from the web browser, the website starts encrypting all the traffic it sends back to the web browser using this encryption key. When the web browser receives the encrypted information back, it uses the encryption key to decrypt the information and display it.
Conclusion
HTTPS provides protection against eavesdropping and stealing sensitive information, including protection from the VPN services used. However, bad VPN choices can still lead to information being stolen through the use of spyware that some of these bad VPNs can install as part of their installation process. So, it is vitally important a good and reputable VPN is used to protect your privacy and information.

